NFC Tags
NFC Tags Manufacturer
-
Offer Good Price
-
Manufacturing various NFC tags
- 1-year quality warranty
- Free return

Professional NFC Tags manufacturer
Custom bulk of different types of NFC tags from China supplier, you have a variety of choice at cheap wholesale price. Reduce your cost and increase efficiency, enjoy benefit business.
RFID tag Maker provide NFC tags, NFC stickers, NFC card, NFC inlays, or NFC discs tag. As well as other NFC products such as NFC wristbands, NFC keychains, NFC business cards, NFC laundry tags, and even NFC drink mats, you can buy all best NFC tag products as below at best wholesale price.
Custom by NFC Tag Feature
Buy NFC tag sticker
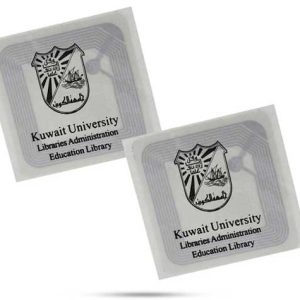
RFID Tag Maker is a Chinese NFC tag sticker factory. NFC (Near Field Communication) tag sticker is a small, adhesive label that contains an NFC chip and antenna. It is a passive device that can be read and programmed using an NFC-enabled device such as a smartphone or a dedicated NFC reader. NFC tag sticker are commonly used for a variety of applications, such as asset tracking, product authentication, and contactless payments. They are easy to attach to a wide range of surfaces and materials, and can be programmed to store and transmit information such as serial numbers, product information, or payment data. Overall, NFC sticker tags offer a simple and cost-effective way to add NFC functionality to a wide range of products and applications.See below more NFC tag sticker and contact us for free samples and quotation.
Our collection of NFC tag sticker covers an extensive spectrum to cater to every need. We exclusively employ official and original Integrated Circuits, popularly known as chips, sourced from NXP (Mifare, NTAG213, NTAG215, NTAG216).
RFID tag Maker take pride in offering not only stock NFC tag Stickers but also bespoke printed options to meet specific requirements. With over a decade of experience, we are well-equipped to fulfill large volume orders, ensuring quality, shape, type, and branding are impeccably maintained. Don’t hesitate to reach out for any bespoke or volume-related inquiries; we’re here to help.
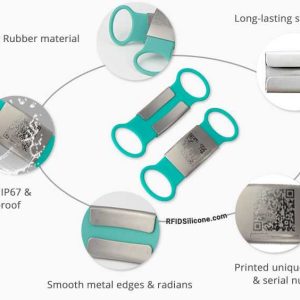
Custom Anti-metal NFC tag
Custom anti-metal NFC tag from profesional Chinese manufacturer. The anti-metal NFC tag, also known as an on-metal NFC tag or metal-mount NFC tag, is a type of NFC (Near Field Communication) tag that can be used on metal surfaces. Standard NFC tags cannot be read accurately when placed directly on metal because the metal surface can interfere with the signal.
Anti-metal NFC tags, however, are designed to work effectively on metal surfaces by using a special material or design that helps to reduce interference from the metal. This allows the tags to be used for a variety of applications, such as asset tracking on metal surfaces, inventory management, and anti-counterfeiting measures.
Custom NFC wristband
China factory, RFID Tag Maker’s NFC wristbands are available in a range of shapes, sizes, and materials, such as silicone, plastic, and fabric. RFID Tag maker is a professional NFC wristband manufacturer.They can be customized with branding or logos, and some are even waterproof, making them suitable for use in swimming pools, water parks, and other wet environments.
NFC wristbands is types of NFC (Near Field Communication) tags that can be used for a variety of applications.
NFC wristbands are commonly used for access control, cashless payments, and event ticketing. For example, at music festivals, attendees may be given an NFC wristband that serves as their ticket and allows them to purchase food, drinks, and merchandise without the need for cash or cards. NFC wristbands can also be used for tracking attendance and managing crowds at events.
NFC wristbands can be read and programmed using an NFC-enabled device, such as a smartphone or a dedicated NFC reader. The wristbands typically operate at a frequency of 13.56 MHz and have a read range of up to a few centimeters.
Customized NFC Keyfob
RFID Tag Maker your one-stop NFC supplier for diversity of NFC keyfobs, save your time and money. We can make suggestions if you detailed discribe the application of NFC key fob.
NFC keyfob is a small, keychain-sized device that contains an NFC chip and an antenna. It is commonly used for access control, cashless payments, and loyalty programs, and can be read and programmed using an NFC-enabled device such as a smartphone or a dedicated NFC reader.
NFC keyfobs are designed for convenience and security. They are easy to carry around and can be attached to a keychain or lanyard, making them easily accessible when needed. They are also highly secure, as they can be programmed to grant access only to authorized individuals, and can be deactivated if lost or stolen.
In addition to access control and cashless payments, NFC keyfobs can also be used for a range of other applications, such as loyalty programs, employee identification, and asset tracking. They are available in a variety of shapes, sizes, and materials, making them suitable for a wide range of environments and use cases.
Buy by NFC Tag Forum
RFID Tag Maker is a professional Chines manufacturer of nfc tags, we not only provide preferential wholesale prices, but also help you choose and buy the correct nfc tag according to your application.
RFID Tag Maker produced the Type 2 NFC tag.The NFC Forum Tag Type 2 is compliant with ISO14443A. The NFC Forum Tag Type 2 NFC tag is the most cost-effective option because it provides sufficient functionality at an appropriate price to meet market demands. The NFC Forum Tag Type 2 NFC tag is read-and-write capable and can be configured to be read-only by the user. The NXP® Ntag and MIFARE® ULTRALIGHT series are typical NFC Tag Type 2 ICs. Typical applications for NFC Forum Tag Type 2 NFC tag include low-value transactions and RFID event tickets. Please kindly see RFID Tag Maker produced NFC Forum Tag Type 2 NFC tags, contact us to get price list.
If you want to buy Type 4 NFC tag from China NFC tag factory, then you should contact us, RFID Tag Maker is a NFC tag factory over 15 years, they have rich production experience and the best wholesale price of NFC tags.
The NFC forum Type 4 NFC tag is compatible with ISO14443A and B standards and supports ISO/IEC 7816 security. These NFC ICs are pre-configured during manufacturing and can be either read/written or read-only; NDEF content can also be modified by the user. Typical NFCTag Type 4 ICs are the NXP® Desfire series, and typical NFC Tag Type 4 applications include payment and security.
Although Type 5 was released in 2015, RFID tag Maker has already been producing this kind of NFC tags, we keep up with market demand, improve technology, and produce various trendy nfc tags.
NFC Forum Tag Type 5 NFC tag is based on the RFID technology defined by the ISO/IEC 15693 specification. Originally, the ISO/IEC 15693 standard was created to enable a greater RF operational range than 1.5 meters. NFC Forum decided to support an Active Communication mode that permits data transfer performance comparable to the RFID technologies supported by NFC Forum, but restricts the reading distance at NFC devices. Typical Tag Type 5 ICs include the NXP® ICode series and STMicroelectronics’ ST25TV series. Typical Tag Type 5 applications include library books, packaging, tickets, etc. If you need want to order Type 5 NFC tag, please email us to get free sample and quotation.
Table of Contents
NFC tag chips
Popular NFC Chips
NXP’s NTAG family of chips are by far the most common chips used in mobile applications. Basic details are listed here, and a breakdown of each feature and chip is listed below.
| Chip | Memory | User Memory | Max URL | Scan Counter | Password | Auth | |
|---|---|---|---|---|---|---|---|
| MIFARE Ultralight | 64 | 48 | 40 | ||||
| MIFARE Ultralight EV1 (80byte) | 80 | 48 | 40 | Yes | |||
| MIFARE Ultralight EV1 (164byte) | 164 | 128 | 120 | Yes | |||
| NTAG203(discontinued) | 168 | 144 | 136* | ||||
| NTAG210µ | 64 | 48 | 40 | ||||
| NTAG210 | 80 | 48 | 40 | Yes | |||
| NTAG213 | 180 | 144 | 136* | Yes | Yes | ||
| NTAG215 | 540 | 504 | 492 | Yes | Yes | ||
| NTAG216 | 924 | 888 | 854 | Yes | Yes | ||
| NTAG424 | – | 256** | 240 | Yes | Yes | Yes | |
| NTAG213 TT | tbc | tbc | tbc | Yes | Yes | ||
| ST25TN01K | 256 | 160 | 152 | ||||
| ST25TN512 | 256 | 64 | 56 | ||||
| NTAG426Q | – | 916** | – | Yes | Yes | Yes | |
| NTAG223 | – | 144** | – | Yes | Yes | Yes | |
| NTAG224 | – | 207** | – | Yes | Yes | Yes |
Other NFC chips
Memory and User Memory
Maximum URL
NFC tag size
Let’s be clear. It’s not the NFC tag size that affects the scan distance, it’s the NFC antenna size. The antenna is the coil inside the NFC tag that generates energy and powers the chip. Theoretically, the larger the NFC antenna, the more energy it can collect and the longer the read range. RFID TAG MAKER manufactures different sizes of NFC TAG antennae for different applications.
NFC tag design

NFC tag reading distance
NFC tag scan counter
NFC tag passwords
NFC tag authentication
Common features of NFC tags
4. How do NFC tags work?
4.1 How do NFC authentication tags work?
4.2 Old and New Authentication Tags2
4.3 NFC Authentication Process Explained
4.4 Using NFC authentication tags in apps
4.5 Token authentication keys
5 How secure are NFC authentication tags?
6 How to buy NFC tags ?
If you are not familiar with NFC technology, then you will be confused about what NFC tag you should buy for your project. RFID TAG MAKER has a lot of experience and can help you start your project. We have also put together some useful information about buying NFC tags to help you out.
6.1 NFC TAG memory
6.2 How many NFC tags memory do I need?
6.3 NFC TAG quality
6.4 NFC tag price
6.5 Genuine and counterfeit NFC TAG
7. Which phones support NFC?
Currently, almost all mobile smartphones can read NFC tags, and almost all Android phones can read and encode them. Apple has enabled NFC tag scanning through an app on iPhone 7, 8, and X running iOS 11 or later. The latest iPhone XS/XR, 11, 12, 13, and iPhone 14 models can scan NFC tags natively without an additional app. Android phones can read NFC tags without an app.
8 How to encode NFC tags
8.1 How many information can be stored on an NFC tag?
8.2 Can someone change the data on my NFC tag?
8.3 Can someone change the data on my NFC tag?
9 NFC TAG Applications
9.1 Personal use
• Open a link/URL
• Turn on/off Wi-Fi
• Turn on/off Bluetooth
• Open a preformatted Email
• Save or open a Telephone Number
• Open your Geo Location
• Launch an application
• Display Plain Text
• Open a preformatted SMS
9.2 Marketing
9.3 Asset Management
9.4 Contactless Payments